On April 21 and 22, 2026, during a session of the Senate Armed Services Committee, Admiral Samuel Paparo of U.S. Indo-Pacific Command articulated insights regarding Bitcoin’s potential utility in the realm of cybersecurity for the military. He characterized Bitcoin as a “valuable computer science tool for power projection” and revealed that INCOPACOM is actively operating a Bitcoin node as part of their experimental protocols.
Admiral Paparo’s remarks coincided with a significant geopolitical event, where the Islamic Republic of Iran requested payment in Bitcoin for secure transit across the Strait of Hormuz. His reference to “power projection” aligns with the theories proposed by Jason Lowery, a prominent figure within the Bitcoin community, known for his book Softwar: A Novel Theory on Power Projection, and his role as an MIT Fellow and Special Assistant to the Commander of INDOPACOM.
In his thesis and subsequent book, Lowery elaborated on the cybersecurity advantages of Bitcoin, emphasizing its distinctive capacity to facilitate “power projection” within cyberspace—a domain of national security that traditionally lacks conventional deterrent strategies.
This work has garnered significant attention, sparking both admiration and criticism within the Bitcoin community; however, subsequent to requests from his superiors, the book was withdrawn from circulation. This action has led some to speculate that its contents possess implications significant enough to warrant military discretion.
Understanding Bitcoin’s Unique Contribution to Military Strategies and Power Projection
The Department of Defense’s 2002 Dictionary of Military and Associated Terms defines power projection as “the ability of a nation to apply all or some of its elements of national power—political, economic, informational, or military—to rapidly and effectively deploy and sustain forces from multiple dispersed locations to respond to crises, contribute to deterrence, and enhance regional stability.” In essence, it refers to a nation’s capacity to influence the behavior of other political entities beyond its borders. This influence encompasses a spectrum from diplomatic to economic actions, as well as military capabilities, including long-range missiles, drones, and robust naval forces.
The concept of deterrence plays a critical role in this discourse. The DoD articulates deterrence as “the prevention from action by fear of the consequences,” which arises from the existence of a credible threat of unacceptable counteraction.
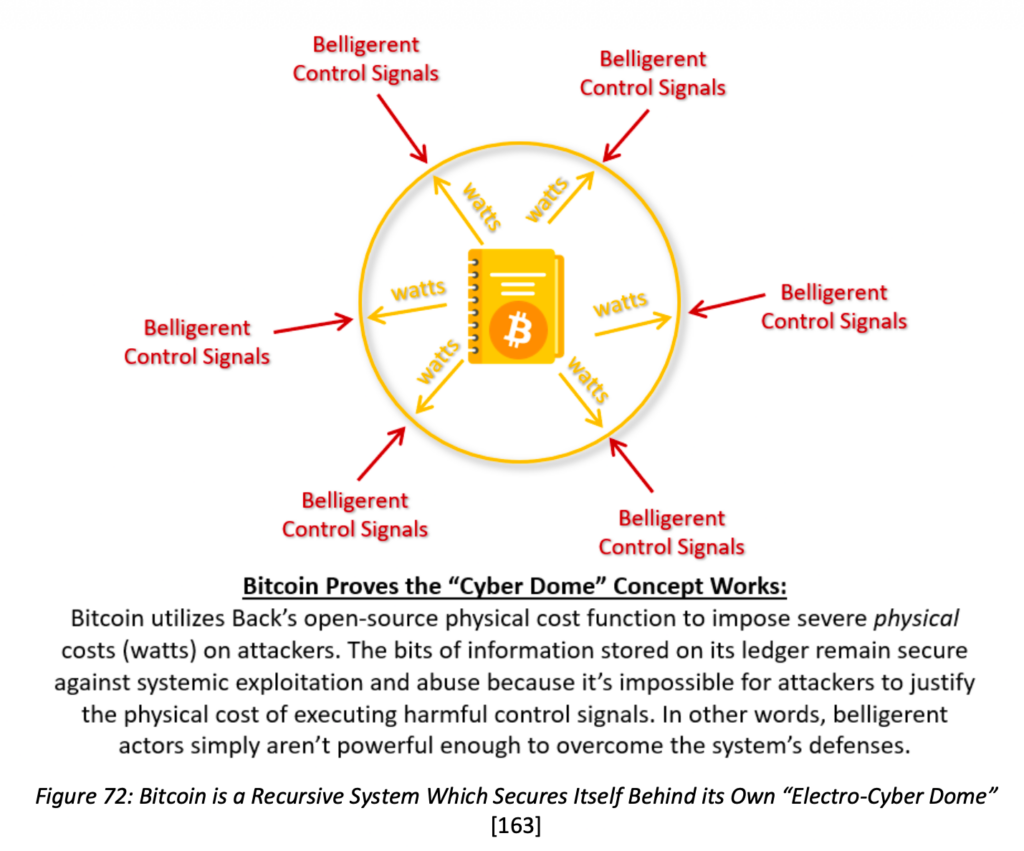
Lowery presents an intriguing perspective by integrating Bitcoin into the physical realm of deterrence. He posits that, akin to microchips serving as conduits for electric power using “encoded logic” within a computer’s motherboard, the global electric grid operates as a “macrochip” that transmits significant quantities of electricity. According to Lowery, Bitcoin mining facilities, which consume substantial energy resources to produce the finite digital asset, function as logic gates within this macrochip, infusing Bitcoin with resilience.
The Security Mechanism of Bitcoin’s Multisignature Wallets
The most evident and powerful exemplification of Bitcoin’s “embedded logic” security is found in the creation of multisignature wallets, which currently safeguard a considerable portion of Bitcoin wealth.
These multisignature wallets necessitate multiple designated private keys to authorize valid transactions before Bitcoin can be transferred. This feature enables the geographic decentralization of Bitcoin private key storage across varied jurisdictions.
As a result, multisignature systems pose a formidable challenge to hackers, who must breach multiple key pairs across various locations under the constraints of time. The legitimate key holders benefit from having quicker access and can respond rapidly to threats. The complexities involved in compromising multiple keys, alongside countering alarms and safeguards, impose considerable costs on potential attackers. This aspect of multisignature wallets aligns with the prevailing definitions of deterrence and power projection, ensuring that Bitcoin funds remain secure while being readily accessible for transfer globally, bolstered by Bitcoin’s inherent censorship-resistant properties.
This stands in stark contrast to conventional financial systems, where centralized databases may freeze or confiscate legitimate assets, as previously observed in the instances of Cyprus and the United States’ seizure of Russian treasury reserves held abroad.
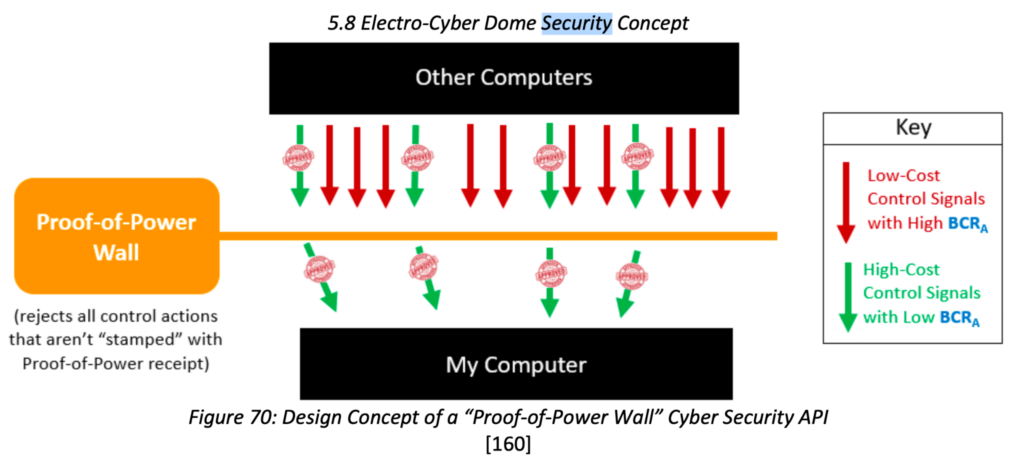
While Admiral Paparo’s comments did not explicitly reference Bitcoin as an asset, they alluded to the potential of Bitcoin’s proof-of-work protocol to secure data and networks external to the Bitcoin ecosystem. However, the internal logic governed by Bitcoin script pertains solely to the Bitcoin asset. Therefore, for external networks to derive advantages from Bitcoin’s robust proof-of-work macrochip, some form of anchoring to Bitcoin will be requisite, where Lowery’s thesis begins to encounter challenges. He expands on the discussion with the introduction of the concept he terms as the “Electro-Cyber Dome.”
Addressing Cybersecurity Threats through the Electro-Cyber Dome
In Software 2.5, Lowery discusses how “software system security vulnerabilities stem from inadequate constraints on the control signals” directed towards networked machines. An instance of this could involve fraudulent login attempts that deplete server resources more than the cost incurred by the attackers. Lowery contends that such vulnerabilities can be exploited, resulting in software being placed in insecure or hazardous states. Examples of prominent network security exploits include:
- Email spam and comment spam — inundation of inboxes or forums with irrelevant messages.
- Sybil attacks — generation of numerous counterfeit identities to manipulate systems.
- Bots and troll farms — automated or coordinated accounts elevating malicious behaviors.
- Weaponized misinformation/disinformation campaigns — saturating networks with fabricated or distorted information.
- Distributed Denial-of-Service (DDoS) attacks — overwhelming bandwidth by flooding networks with excessive service requests.
- Forged or replayed control signals — simulating legitimate commands that compromise software security.
- Systemic exploitation of administrative permissions/insider abuse — leveraging trust-based hierarchies to compromise high-privilege accounts.
Lowery suggests that alternative networks could enhance their defenses against these threats through the adoption of proof-of-work (POW) protocols akin to Bitcoin’s.
In the original Bitcoin white paper, Satoshi Nakamoto defines Bitcoin’s proof-of-work succinctly: “The proof-of-work involves scanning for a value that, when hashed using SHA-256, the hash commences with a specific number of leading zero bits. The required level of work grows exponentially with the number of zero bits needed, and can be authenticated by executing a single hash.”
Nakamoto draws a connection to Adam Back’s “Hash Cash, A Denial of Service Counter-Measure,” which aimed to deter email spam by mandating that senders produce a POW stamp of difficulty designated by the email’s recipient. Recipient servers would keep a registry of used stamps to prevent the reuse of work by attackers, addressing “double-spending” incidents. However, these stamps lacked transferability—an aspect pursued by certain cypherpunks in their quest for digital currency. Hal Finney further advanced the field with the invention of Reusable Proof of Work (RPOW).
RPOW effectively tokenized POW stamps through a centralized server, enabling tracking and transfer facilitation. A pivotal innovation by Nakamoto was to decentralize this server and its list of spent stamps within the blockchain framework while also establishing a universal difficulty algorithm that all Bitcoin miners must adhere to, as opposed to individual, variable difficulty targets determined by distinct websites.
In his concept of the Electro-Cyber Dome, Lowery essentially revisits Hash Cash principles. He specifies that servers may identify their desired difficulty targets, while not explicitly asserting that the Dome must utilize Bitcoin’s SHA-256 protocol. Despite this, Bitcoin serves as a primary illustration of how a cybersecurity framework can operate effectively at scale: “Our understanding of electro-cyber domes as functional security protocols is derived from Bitcoin’s mechanisms for safeguarding its information against systemic exploitation.”
Lowery additionally asserts that as such systems gain traction, a paradigm of aggression could emerge from substantial miners. He notes: “It should be highlighted that this would not solely represent a ‘defensive’ power projection capability… Those possessing access to proof-of-power could potentially ‘breach’ these electro-cyber dome defenses if they choose. Therefore, proof-of-power protocols are not exclusively ‘defensive’ as some contend. A major threat to entities employing physical cost function protocols like Bitcoin is other individuals utilizing the same protocol (which is why Nakamoto references the term ‘attack’ 25 times within an 8-page white paper, invariably concerning individuals executing the same protocol).”
Critiques of Lowery’s Softwar Thesis
Broadly, detractors challenge the notion that data or networks external to Bitcoin can be secured through Bitcoin’s technological framework, encompassing its POW, blockchain, or native asset. Jameson Lopp conducted an extensive evaluation of Lowery’s thesis and book, articulating admiration for several aspects while ultimately dismissing its overarching conclusions by stating: “Softwar falls short of providing a blueprint for future development.”
A prevailing question arises regarding the sensibility of employing SHA-256 proof of work to safeguard access to networks that exist outside Bitcoin; the validity of this approach is questionable. Should the Electro-Cyber Dome not impose a sufficiently high POW difficulty for mining Bitcoin, or if it does not utilize Bitcoin’s specified difficulty, asset, or blockchain, can it truly be termed a utilization of Bitcoin?
Moreover, considering that China dominates the ASIC manufacturing sector for Bitcoin mining, it seems imprudent for INDOPACOM—the U.S. military division responsible for maintaining order within the Indo-Pacific region—to rely on algorithms that China produces in abundance for brute-force attacks. Such a decision appears misplaced and may prompt a consideration of alternative POW algorithms. At this juncture, they would no longer be employing Bitcoin, thus undermining the macrochip assertion. Instead, this would simply revert to classic Hash Cash principles. Lowery’s association with Bitcoin may serve primarily as a strategic marketing approach and a nod towards a community that inspired him, rather than representing the ultimate tool that INDOPACOM might prefer to utilize.
A Middle Ground Perspective
Amidst the theoretical, practical, and critical discourse surrounding Software-style ideas, emerging projects exemplify how Bitcoin may extend its security capabilities beyond mere financial transactions.
SimpleProof, an Open Time Stamps-centric Bitcoin notary, has leveraged the blockchain to document hashes of data, affirming that a particular version existed at a specific time. This application of Bitcoin as a time-stamping service proved pivotal in safeguarding one faction during the Guatemalan elections against allegations of fraud, resulting in tangible political ramifications for the nation.
Conversely, Michael Saylor spearheaded the development of what is referred to as the Orange Checkmark protocol, a privacy-preserving, Bitcoin-native decentralized digital identity system. Despite initial intrigue within the Bitcoin community upon its announcement a few years prior, it has yet to achieve widespread adoption.
Intriguingly, Jameson Lopp—perhaps one of Lowery’s most vocal critics, having authored three dedicated articles on the subject—implemented a proof-of-work-based spam protection mechanism on his website’s submission form, which, according to Lopp, has been effective. If he can recognize the utility of these foundational concepts, even if they merely align with Hash Cash, it suggests a future where Bitcoin-like technologies could indeed safeguard networks and data on a broader scale.
Thank you for visiting our site. You can get the latest Information and Editorials on our site regarding bitcoins.